AI based security: Protecting AI systems and their valuable information from attacks and vulnerabilities requires AI-based security. The integrity and confidentiality of AI processes are crucial in a future that relies on AI for decision-making and data processing.
This definition describes ways to improve AI-based security to protect information, compartmentalize AI operations to reduce the risk of attack, and adopt a zero trust approach.
What is AI Based security?
Protecting the information generation process: Secure the entire AI lifecycle, from data collection and model training to deployment and ongoing operations, to protect the information generation process. Information generation requires rigorous protection of both the data and the AI system models that transform data into actionable insights.
AI process compartmentalization: Use compartmentalization or segmentation to improve the security of AI processes. This involves separating and restricting phases of the AI workflow. Protecting critical training data and model parameters helps prevent manipulation. Compartmentalization reduces the impact of breaches.
A zero-trust model: this security strategy is based on the principle of no implicit trust, even for users and internal systems. By continuously verifying people and systems, this paradigm supports AI-driven security . AI systems can be extensively evaluated in terms of reliability, authentication, and authorization.
Improving AI-based security using these key points is equivalent to leveraging AI itself:
- Machine learning for anomaly detection: Thanks to AI, complex anomaly detection systems can monitor AI processes to detect any unusual behavior. This facilitates the detection of and response to security events.
- Behavioral analysis: AI can create basic patterns and detect variations that may indicate security vulnerabilities by monitoring user and system behavior.
- Secure model deployment: AI can automate the deployment of models in secure containers, monitoring and restricting access to models to authorized people and processes.
- Real-time monitoring and threat intelligence from AI-driven cybersecurity solutions help businesses stay ahead of emerging threats and vulnerabilities.
AI-driven security is evolving to protect the AI lifecycle, information, and data. Organizations can protect their AI systems from various risks and vulnerabilities by compartmentalizing AI processes, adopting a zero-trust architecture, and using AI technologies to enhance security. This ensures the reliability and credibility of AI-guided information.
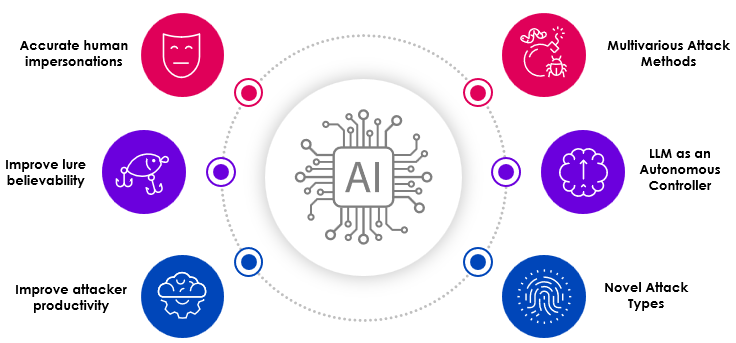
What types of attacks or risks do AI face?
What is AI Based security? It is essential to identify and address the different types of attacks and risks that can compromise the integrity and reliability of AI models and systems.
- Data security risks – the AI pipeline as an attack surface: The entire data pipeline is vulnerable to attack since AI systems rely on data. This includes data collection, storage, and transfer. Attackers can exploit these processes to gain access, modify data, or introduce malicious input.
- Data security risks – production data in the engineering process: Using real-world production data in AI engineering is risky. If not handled properly, sensitive production data could end up in model training datasets, creating privacy breaches, data breaches, or biased model outputs.
- Adversarial attacks on AI or machine learning models: Adversarial machine learning attacks mislead AI models by altering the input data. Attackers can subtly modify visual or textual elements to generate an erroneous classification or prediction. These attacks can compromise the reliability of AI systems.
- Data poisoning attack: Data poisoning involves inserting harmful or misleading data into training datasets. This corrupts the learning process, resulting in biased or underperforming models. Attackers exploit the AI’s decision-making to cause harm.
- Input manipulation attack: Real-time input manipulation attacks modify the inputs to the AI system. They alter sensor readings, parameters, or user inputs to change the AI’s responses or actions. These attacks could prevent AI-powered systems from functioning and lead to poor decisions.
- Model inversion attacks: Model inversion attacks reverse-engineer AI models to steal sensitive data. Attackers use model outputs to infer sensitive training data, creating privacy risks and potential breaches.
- Membership inference attacks: In membership inference attacks, adversaries attempt to determine whether a specific data point was part of the AI model training dataset. This can expose private data relating to individuals or organizations.
- Exploratory attacks: Exploratory attacks probe AI systems to understand their underlying workings. Attackers can use searches or inputs to detect vulnerabilities, behavioral patterns, or proprietary information for later attacks.
- Supply chain attacks: The development and deployment of AI systems are targeted by supply chain threats. Attackers hack software or hardware to insert malicious code or gain access to AI resources, including third-party libraries or cloud services.
- Resource exhaustion attacks: Resource exhaustion attacks overload AI systems with requests or inputs, degrading performance or creating downtime. These attacks could reduce the availability of AI services.
- Risks of fairness and bias: Decisions made by AI models can perpetuate prejudice and discrimination. AI systems can create unfair outcomes or promote social biases, thus raising ethical, reputational, and legal issues.
- Model drift and degradation: Data distribution, threats, and technological obsolescence can reduce the effectiveness of AI models over time. This threatens the accuracy and reliability of AI systems, especially in dynamic environments.
Understanding these threats and dangers is essential in order to implement AI security measures and reduce vulnerabilities in AI models and systems.
How can I implement a process or standard to protect my business?
We want to present and explain the different types of standards currently in force. We also want to show how we can deploy them across the company.
Current standards
- ISO/IEC 27001 is the world’s most well-known standard for Information Security Management Systems (ISMS). It defines the requirements that an ISMS must meet.
- ISO/IEC FDIS 5338 – The ISO/IEC/IEEE 12207 standard describes software lifecycle processes, and the ISO/IEC/IEEE 15288 standard describes system lifecycle processes. While these lifecycle processes are broadly applicable to AI systems, they require the introduction of new processes and the modification of existing ones to accommodate the characteristics of AI systems.
- SAMM – SAMM stands for Software Assurance Maturity Model. Our mission is to provide an effective and measurable way for all types of organizations to analyze and improve their software security posture. We aim to raise awareness and educate organizations on the design, development, and deployment of secure software through our self-assessment model.
How can we apply these standards to our organization?
- Standardization of processes: ISO/IEC standards provide a framework that enables the CTO or CIO to streamline and standardize processes within the company, thereby ensuring consistency and efficiency of technology operations.
- Improving information security: By implementing the ISO/IEC 27001 standard, the CTO or CIO can establish a robust information security management system, identifying and mitigating risks, protecting sensitive data and ensuring compliance with legal and regulatory requirements.
- Ensuring quality management: The ISO 9001 standard can be applied by the CTO or CIO to implement quality management processes within the company. This involves defining objectives, monitoring performance, and continuously improving processes, thereby optimizing customer satisfaction.
- Fostering a culture of continuous improvement: The CTO or CIO can use ISO/IEC standards to encourage a culture of continuous improvement within the organization. By implementing ISO 9001 and ISO 27001, regular audits and reviews can be conducted to identify areas for improvement and drive innovation.
- Facilitating international collaboration and partnerships: Adherence to ISO/IEC standards provides a common language and framework that facilitates collaboration and partnerships with other companies. The CTO or CIO can thus guarantee interoperability, the exchange of best practices, and ensure seamless integration with partners and customers worldwide.
- Evaluate and analyze gaps: Conduct a comprehensive evaluation and analysis of gaps within your procedures and safety measures. Identify areas for application and optimization of ISO/IEC and SAMM standards.
- Leadership commitment: Secure the support and commitment of senior management, including the CTO, CIO, and other key stakeholders. Their commitment is essential for organization-wide adoption of these standards.
- Customization and integration: Tailor the standards to your organization. Ensure seamless integration into workflows. The unique properties of AI systems may require process adjustments to ISO/IEC FDIS 5338 and 15288 standards.
- Employee training and awareness: Invest in employee training and awareness initiatives to ensure team members understand and embrace these standards. SAMM’s self-assessment technique helps teams learn best practices in software security.
- Documentation and rules framework: Comprehensive documentation, including rules describing standards and processes, is necessary. This encompasses task assignment, process documentation, and the implementation of information security and software assurance standards.
- Methodical implementation and testing: Gradually establish security standards and measures within your organization. Test and validate these standards to ensure they are properly implemented and meet objectives.
- Continuous monitoring and improvement: Implement regular audits and reviews to monitor compliance with standards. Enhance software security, quality, and assurance by identifying and resolving issues.
- Certification and accreditation: plan to acquire ISO/IEC 27001 certification to demonstrate your commitment to information security.
- Communication and reporting protocols: establish explicit ways to report incidents, quality issues, and progress updates.
- Gradual implementation across all business units: progressively extend the adoption of these standards to different departments and units.
- Collaboration with external experts: collaborate with external experts or consultants who are proficient in ISO/IEC and SAMM standards and can guide you through the implementation process.
How is AI used in security?
Artificial intelligence (AI) is increasingly being used in various aspects of security to improve threat detection, incident response, and overall cybersecurity. Here are some of the main ways AI is being used in the security field:
- Advanced threat detection:
- Anomaly detection: AI identifies unusual patterns, signs of potential threats.
- Behavioral analysis: monitors user and network behavior to detect suspicious activities.
- Signatureless detection: recognizes new and unknown threats based on malicious behavior.
- Network protection:
- Intrusion detection and prevention: AI detects intrusions on the network and responds quickly.
- Firewall optimization: analyzes network traffic to optimize firewall rules and identify vulnerabilities.
- Improved terminal security:
- Endpoint protection: AI-based antivirus and anti-malware detect and prevent malware-induced infections.
- Zero-day threat detection: Identifies unknown threats by monitoring endpoint behavior.
- User authentication and access security:
- Biometric authentication: AI enables secure access through biometrics.
- Behavior-based authentication: analyzes user behavior patterns to detect unauthorized access.
- Optimizing security operations:
- SIEM Enhancement: AI automates threat analysis, alert prioritization, and incident response for SIEM platforms.
- Chatbots and virtual assistants: AI helps security analysts identify and mitigate incidents in real time.
- Phishing and fraud prevention:
- Email security: AI analyzes email content and sender behavior to detect phishing and malicious emails.
- Transaction monitoring: highlights suspicious financial transactions and indicators of fraud.
- Vulnerability management:
- Automated analysis: AI automates the analysis and assessment of vulnerabilities.
- Risk assessment: AI assesses the severity and impact of vulnerabilities in order to prioritize fixes.
- Security automation and orchestration:
- Automating incident response: AI-driven workflows automate responses to common security incidents.
- Orchestration: AI coordinates security processes governing responses to complex threats.
- Predictive threat analysis:
- Threat intelligence: AI analyzes threat intelligence feeds to predict emerging threats and vulnerabilities.
- Improved physical security:
- Surveillance: AI-driven video analytics identifies suspicious activity to improve physical security.
- Automation of compliance and reporting:
- Audit and compliance: AI helps automate compliance checks and generate reports to meet regulations.
- Secure software development support
- Static and dynamic code analysis: AI analyzes code to identify security vulnerabilities during development. Continuous monitoring, updates, and training are essential to stay ahead of evolving threats.
How does AI improve security?
Artificial intelligence (AI) enhances security by improving threat detection, response capabilities, and overall cybersecurity measures in the following ways:
- Advanced threat detection and real-time monitoring:
- AI analyzes data looking for unusual patterns and behaviors, enabling early threat detection.
- Real-time monitoring and alerts enable the rapid identification and response to security incidents.
- Reducing false positives: AI minimizes false alarms, allowing security teams to focus on real threats.
- Threat intelligence and predictive analytics: AI processes threat assessment data and predicts emerging threats, thereby strengthening proactive defense measures.
- Effective incident response: Automation accelerates incident response, including isolation and corrective system updates.
- Protection against phishing and zero-day vulnerabilities: AI detects phishing attempts and zero-day vulnerabilities, thus improving email and system security.
- User authentication and access control: AI enables secure authentication methods and continuously monitors user behavior.
- Vulnerability management and compliance: AI automates vulnerability assessment, risk prioritization and compliance controls.
- Security automation and physical security: AI-based automation streamlines security processes and improves physical surveillance.
- Secure software development: AI identifies and mitigates code vulnerabilities during development.
By leveraging AI, organizations strengthen security, react more quickly to threats, reduce risks, and adapt effectively to evolving cybersecurity challenges.
Will AI take control of cybersecurity?
Machine learning in cybersecurity and artificial intelligence in risk management are powerful tools that significantly improve security measures and risk mitigation efforts. However, it’s important to clarify that these are tools used by cybersecurity professionals rather than substitutes for human expertise. Here’s why:
- AI augments human expertise: AI strengthens cybersecurity by automating tasks, optimizing threat detection, and reducing response times.
- Advanced threat detection: AI identifies sophisticated threats, including zero-day vulnerabilities and insider attacks, thereby improving overall security.
- Behavioral analysis and continuous monitoring: AI performs behavioral analysis, identifies unusual activities and enables real-time threat monitoring.
- Effective threat response: AI automates routine tasks, allowing security teams to focus on complex challenges and strategic decisions.
- Adaptability, speed and threat intelligence: AI adapts to data analysis, responds in real time and processes vast amounts of threat assessment data.
- Security orchestration: AI-powered automation streamlines incident response and mitigation processes.
- Challenges and human expertise: AI faces adversarial attacks and cannot replace human judgment and ethical considerations in cybersecurity.
AI enhances human expertise in cybersecurity. It operates by automating tasks, optimizing threat detection, making responses more effective, and addressing the fluctuating challenges of the digital landscape.