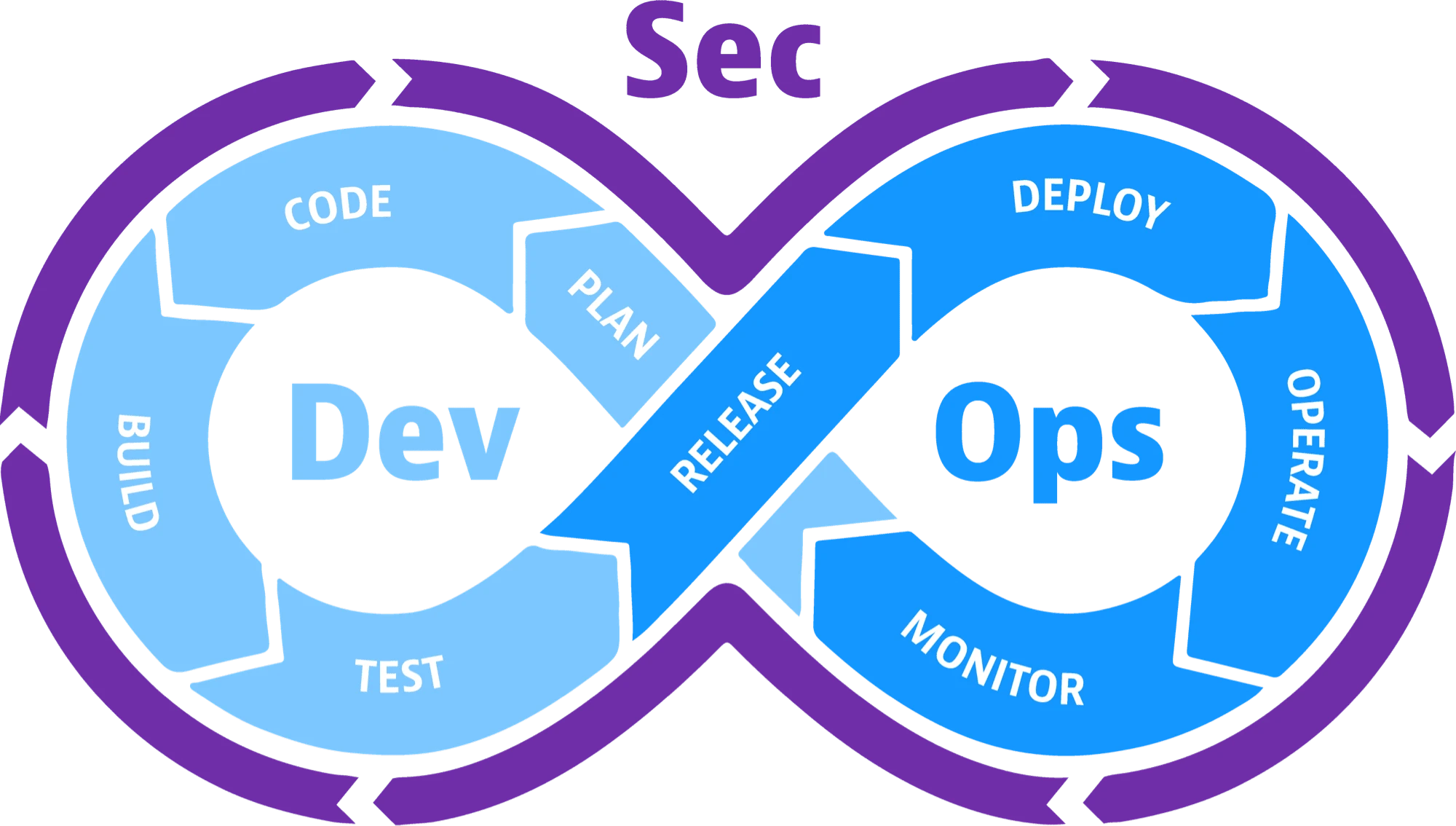
Definition of DevSecOps
DevSecOps stands for development, security, and operations. Essentially, it’s a concept where application security is a shared responsibility across all of IT. The definition of DevSecOps revolves around automatically making security a top priority as part of any software development lifecycle, and continuing this priority even after development is complete.
How to integrate security into a DevOps framework
To integrate DevSecOps into the DevOps workflow, you must systematically incorporate security design, checks, and balances throughout the development process. In this way, DevSecOps also represents a significant cultural shift.
In a traditional application development framework, the DevOps team would rely on the security team to find vulnerabilities. They would then take the security team’s feedback and incorporate it into the next round of application changes. By joining forces with the security team from the outset, security becomes part of the original solution, and developers have a better chance of producing a secure application within the first few iterations.
The integration process involves the following:
- Automation: Many security processes can be automated, avoiding manual, repetitive, and time-consuming entry.
- Code analysis: Security experts can analyze the code that developers write to identify potential vulnerabilities.
- Periodic threat assessments: As application development progresses, the threats to which it is vulnerable are subject to change. Regularly assessing potential threats allows the team to incorporate security at one stage before moving on to the next. This also prevents the team from having to go back and change a fundamental element of the application, which, in some cases, might require altering later aspects of the program.
- Configuration tracking: If the configuration of an application element changes, or how the application interacts with others changes, this should be known and tracked. This is because every configuration change could introduce vulnerabilities.
- Security training: While many developers have a basic understanding of security principles and techniques, more in-depth training is necessary. Understanding the inner workings of security threats and solutions will help them better integrate security into the development process.
Application security tools used in DevSecOps
The DevSecOps process cannot be accomplished without the aid of tools. A variety of tools, including SAST, SCA, IAST, and others, enable DevSecOps, both as a concept and a process, to be as valuable as possible.
Static Application Security Testing (SAST)
SAST tools are most commonly deployed during the coding phase of a systems development lifecycle. After coding, SAST will also review that code as part of a build and deployment process. SAST tools are powerful because they can scan proprietary or custom code for any type of design flaw or coding error.
Software composition analysis (SCA)
The concept behind a Security Awareness (SCA) tool is to scan source code, as well as binaries, for vulnerabilities. Known vulnerabilities are all too common throughout an application’s lifecycle. Open source and third-party components can harbor these vulnerabilities, creating opportunities for exploitation by cybercriminals. SCA tools will enable integration as part of a continuous deployment pipeline to continuously identify known vulnerabilities.
Interactive Application Security Testing (IAST)
Testing is critical as part of any system development lifecycle. With IAST tools, you’re implementing tools that will work alongside manual or automated functional testing. These tools analyze the runtime behavior of a web application and, in doing so, can identify vulnerabilities, giving developers access to the source of the problem.
Dynamic Application Security Testing (DAST)
DAST is a type of automated testing technology unique in its application. By using a DAST tool , you act as if you were a cybercriminal as you navigate through an API or web application. Observing how the application renders on the client side, over a network connection, can help identify vulnerabilities that need patching. DAST is not only useful for web applications but also for web-connected devices such as IoT devices, back-end servers, and more.
Why is DevSecOps important?
DevSecOps is important because, as companies produce more software at a faster pace and in more complex environments, the likelihood of security failures increases exponentially. The speed at which code is released increases security vulnerabilities in the pipeline.
Cloud-native technologies are not well-suited to static security policies. Their architectures and components (serverless, microservices, containers within microservices) offer developers greater flexibility, but also greater complexity from a security perspective. The importance of cloud security , coupled with the increasing need to iterate faster than ever before and heightened cybersecurity concerns , means that DevOps is forced to adapt. This new development landscape is why DevSecOps is both valuable and necessary.
Furthermore, by increasing efficiency and ensuring better software security, DevSecOps is important to users. Faster delivery of a more secure product translates into customer satisfaction, which has implications for the bottom line. DevSecOps not only helps optimize compliance by supporting a more proactive security posture, but it also signals to the customer that security is paramount to the service or product provided.
Benefits of DevSecOps
DevSecOps allows a development team to deliver and deploy code quickly without sacrificing security. This results in several additional benefits.
Save time
Delivering code quickly is easy enough. A DevOps team could write the code and release it, often without noticing or even ignoring potential security issues. However, over time, vulnerabilities that weren’t addressed during the development process can resurface and haunt the organization, the development team, and the users the application is intended to serve. This would likely result in developers having to waste time going back and addressing the security problems.
With security operations as an inherent part of the development process, vulnerabilities are addressed at every design stage. Therefore, the development team can release a more secure iteration of the program faster.
Cost reduction
Security issues can cause costly and time-consuming delays. The person-hours required to develop an application increase significantly when developers have to go back and rewrite much of the code to address vulnerabilities. This not only means more time spent on a project, but it also prevents those same professionals from working on other projects that could benefit the organization’s bottom line.
If an organization uses a DevSecOps lifecycle, on the other hand, the need to go back and make changes can be significantly reduced, conserving people’s hours and freeing up the development team to engage in other work.
Furthermore, this could lead to a better return on investment (ROI) for your security infrastructure. As the security team addresses issues early in the design process, their work prevents many future problems. This not only results in a more secure application but also reduces the number of issues your security infrastructure will have to deal with in the future.
Proactive security
Vulnerabilities in code can be detected early by implementing a DevSecOps approach. The DevSecOps model involves analyzing code and conducting regular threat assessments. This proactive approach to security allows teams to take control of an application’s risk profile instead of simply reacting to issues as they arise, especially those that would have been detected during threat assessments.
Continuous feedback
DevSecOps creates a continuous feedback loop that integrates security solutions throughout the software development process. Whether your DevOps is delivered on-premises or in the cloud, developers receive constant feedback from the security team. Similarly, the security team receives ongoing feedback from developers, which they can use to design solutions that better fit the application’s infrastructure and functionality.
Continuous feedback also improves the development of automated security features. The security team can gather information about the application’s workflow from the development team and use that feedback to design automation protocols that benefit specific processes for that exact application.
Furthermore, continuous feedback allows the team to schedule alerts that indicate the need for adjustments to the application design or its security features. Understanding what each team needs to know and how it impacts the application development process can be used to determine the various conditions that should trigger different alerts. With well-designed secure DevOps automation, the team can produce secure products in less time.
Create collaboration between teams
A more collaborative environment is one of the cultural benefits of a DevSecOps approach. Throughout the entire development lifecycle, communication is improved because team members need to understand how every facet of an application interacts with the necessary security measures. As different teams combine their thinking to solve this puzzle, collaboration increases, ultimately resulting in a more cohesive organization and product.
DevSecOps Challenges
The implementation of DevSecOps, despite its benefits, can potentially present some challenges.
Incorporating DevSecOps into the team
isn’t just about a new tool; it’s a cultural shift. Any cultural change can encounter resistance, especially when it affects how teams are accustomed to working. DevSecOps aims to break down silos, requiring operations and development to embrace the notion that security is also their concern and responsibility.
An additional element in the challenge of getting teams on board is the need to develop new skills. Development and operations teams need to acquire security skills, and vice versa. This can be resource-intensive, and some organizations may struggle to find or train people to acquire these new skills. Training and education are key components for a successful DevSecOps implementation.
Integrating new technologies
: Automation, which is key to DevSecOps, requires new toolsets for security testing and monitoring. These tools must be compatible with existing environments, and this can be time-consuming and resource-intensive for both ITDMs and their teams. Automation itself is also time-consuming. It must be set up, tested, and then maintained for a successful DevSecOps workflow. Like tool integration, automation requires an additional skill set or a team reorganization, which can be challenging in certain organizations.
Achieving compliance
, while ultimately a benefit of DevSecOps, can be challenging without sacrificing agility. This requires an additional level of expertise or extra effort from the team to maintain agility while ensuring regulatory compliance.
While these challenges may discourage organizations from adopting DevSecOps, they actually make a strong case for the methodology. Establishing collaboration between teams to overcome and resolve these challenges is key to successful adoption and a well-implemented workflow.
Five tips for selecting a DevSecOps tool
While there are several tools available on the market for DevSecOps purposes, there are certain capabilities you’ll want to consider when selecting the right one for your organization.
- Find a tool that integrates seamlessly into your existing systems and workflows.
- Look for a tool that can provide complete observability of all your logs, metrics, app performance, and security.
- Find a tool that can monitor, measure, and analyze every step of your CI/CD pipeline.
- Look for a tool that protects, monitors, and reports on container deployment and orchestration.
- Look for a tool that can scale at the same pace as you.
DevSecOps Best Practices
To fully benefit from the advantages of DevSecOps, consider these best practices for incorporating security into your development and operations workflows.
Test early.
This is the motto and mantra of DevSecOps. Moving security to the beginning of the development process ensures that it becomes an integral part of the workflow and is incorporated throughout the entire development process.
Testing early allows teams to detect vulnerabilities from the outset and address them before they become bigger problems later on. As a result, the development team will think about implementing security for the app as they build it.
Implementing Traceability, Auditing, and Monitoring:
Implementing traceability, auditability, and visibility is key to a successful DevSecOps process because it results in deeper insights. Deeper insights provide actionable information to improve the efficiency, resilience, and overall productivity of the system. Traceability is primarily used for debugging, but it also plays an important role in protecting code during app development and ensuring compliance with regulatory requirements.
Auditing technical, procedural, and administrative security controls is key to compliance. It is essential to have well-documented controls and for all team members to adhere to them.
Monitoring is key to a DevSecOps environment. Having visibility across the entire system and the development lifecycle is crucial for security. Implementing alerts also ensures team accountability, enables faster response to issues, and generally helps teams understand where their work overlaps.
Think about people, processes, and technology.
Implementing DevSecOps starts with people, and therefore, with culture. Education is a crucial component for changing the culture and empowering team members to adopt DevSecOps. Successful change requires strong and effective leadership.
A change in mindset necessitates a change in process: this is required to make room for proactive security testing. Implementing a DevSecOps process may also require new tools and increased automation.
Training, training, training.
Part of adopting a DevSecOps strategy should be robust training. Developers don’t necessarily have security skills, and vice versa for security professionals. Education, both from a cultural and values perspective and from the standpoint of skills, knowledge, and tools, will ensure a successful DevSecOps implementation in any organization.
DevSecOps with Elastic
DevSecOps and Elastic go hand in hand. With its ELK technology stack, Elastic can unify all your data to help you monitor and troubleshoot systems, enabling DevSecOps to work together more efficiently.